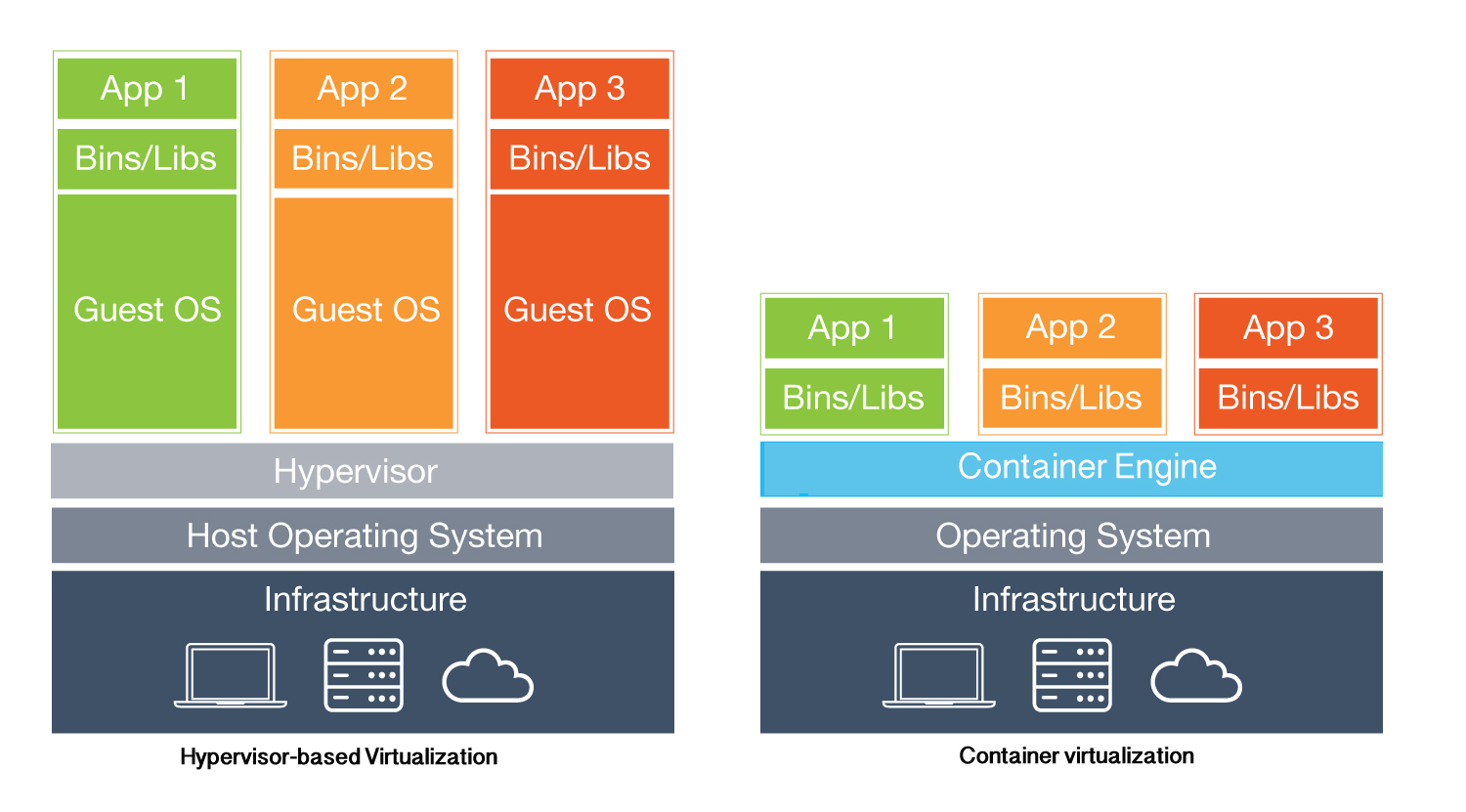
 Virtualization isn’t just for geeks or those who run enormously powerful servers. In its strictest sense, virtualization refers to running two or more operating systems one one physical PC. Either the multiple operating systems run side-by-side, with a separate piece of software called a hypervisor used to manage them, or one operating system runs the other operating systems within a program windows or workspace.
Virtualization isn’t just for geeks or those who run enormously powerful servers. In its strictest sense, virtualization refers to running two or more operating systems one one physical PC. Either the multiple operating systems run side-by-side, with a separate piece of software called a hypervisor used to manage them, or one operating system runs the other operating systems within a program windows or workspace.
CONTAINERIZATION
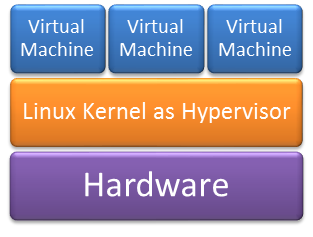
It is an operating-system-level virtualization method for running multiple isolated Linux systems (containers) on a control host using a single Linux kernel, where the Linux kernel provides the cgroups functionality that allows limitation and prioritization of resources (CPU, memory, block I/O, network, etc.) without the need for starting any virtual machines, and also namespace isolation functionality that allows complete isolation of an applications’ view of the operating environment, including process trees, networking, user IDs and mounted file systems. Containerization is lighter for the host resources, in comparison with a full virtualization, hence more suitable for small embedded systems or IoT nodes.
 LXC (Linux Containers) is one of the several Containerization systems available. it provides operating system-level virtualization through a virtual environment that has its own process and network space, instead of creating a full-fledged virtual machine. LXC relies on the Linux kernel cgroups functionality that was released in version 2.6.24. It also relies on other kinds of namespace isolation functionality, which were developed and integrated into the mainline Linux kernel. Originally, LXC containers were not as secure as other OS-level virtualization methods: in Linux kernels before 3.8, the root user of the guest system could run arbitrary code on the host system with root privileges, much like chroot jails. Starting with the LXC 1.0 release, it is possible to run containers as regular users on the host using “unprivileged containers”. Unprivileged containers are more limited in that they cannot access hardware directly. Nevertheless, even “privileged containers” should provide adequate isolation in the LXC 1.0 security model, if properly configured.
LXC (Linux Containers) is one of the several Containerization systems available. it provides operating system-level virtualization through a virtual environment that has its own process and network space, instead of creating a full-fledged virtual machine. LXC relies on the Linux kernel cgroups functionality that was released in version 2.6.24. It also relies on other kinds of namespace isolation functionality, which were developed and integrated into the mainline Linux kernel. Originally, LXC containers were not as secure as other OS-level virtualization methods: in Linux kernels before 3.8, the root user of the guest system could run arbitrary code on the host system with root privileges, much like chroot jails. Starting with the LXC 1.0 release, it is possible to run containers as regular users on the host using “unprivileged containers”. Unprivileged containers are more limited in that they cannot access hardware directly. Nevertheless, even “privileged containers” should provide adequate isolation in the LXC 1.0 security model, if properly configured.
To experiment with Raspberry PI3 , Ubunto and LXC Containers you can start here.
